Everything you need to stop reacting and start deciding.
Built by a defender who lived the pain of manual CVE triage. Import from any scanner, enrich with real exploit intelligence, map to compliance, and act — all in one workflow.
Works with the scanners you already run
Product Tour
A real platform — captured straight from the product
Screenshots from the live CVERiskPilot demo workspace. Every view is interactive at cveriskpilot.com/demo.
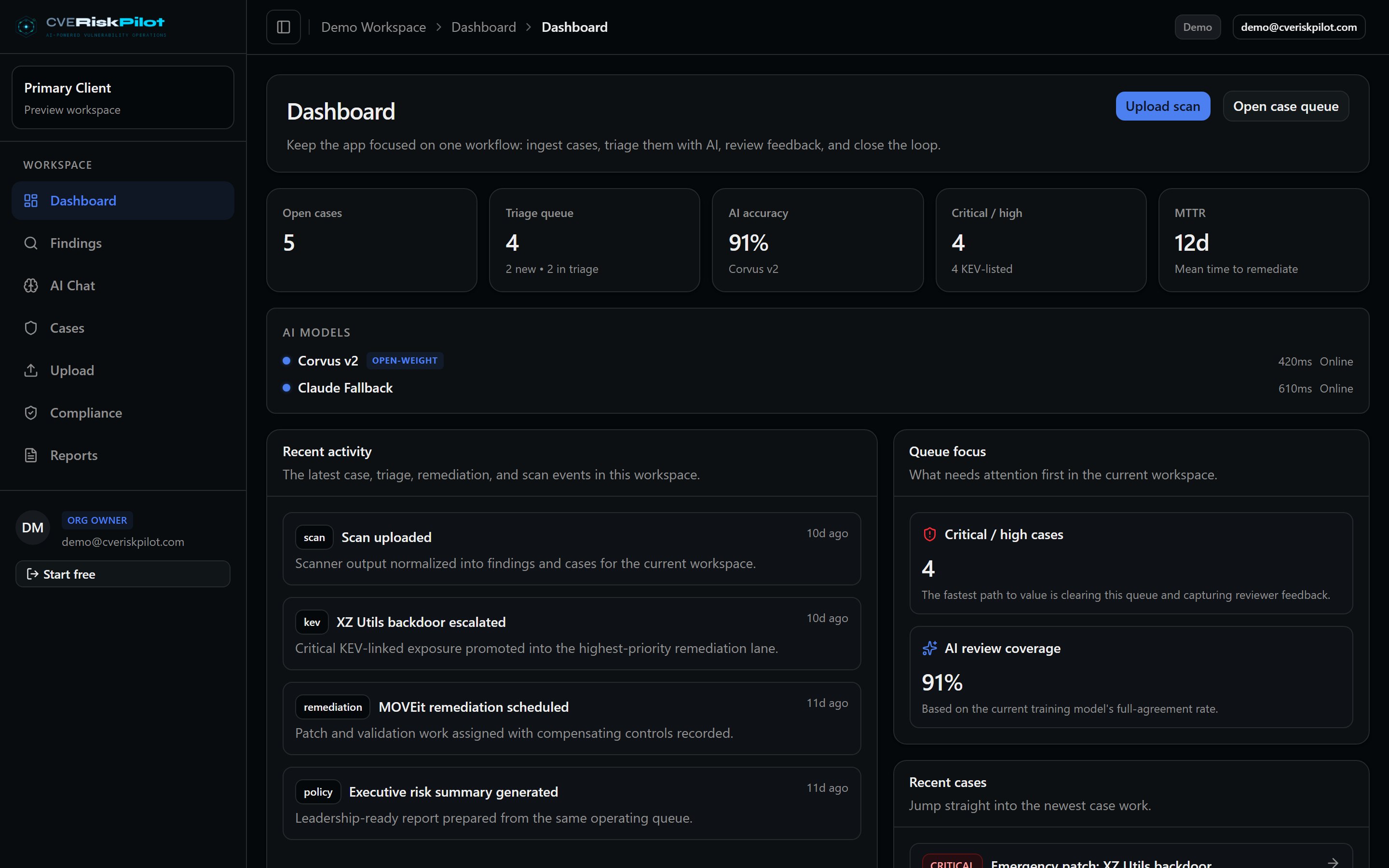
Executive dashboard
Real-time posture — open findings, KEV exposure, SLA compliance, severity breakdown.
Open live view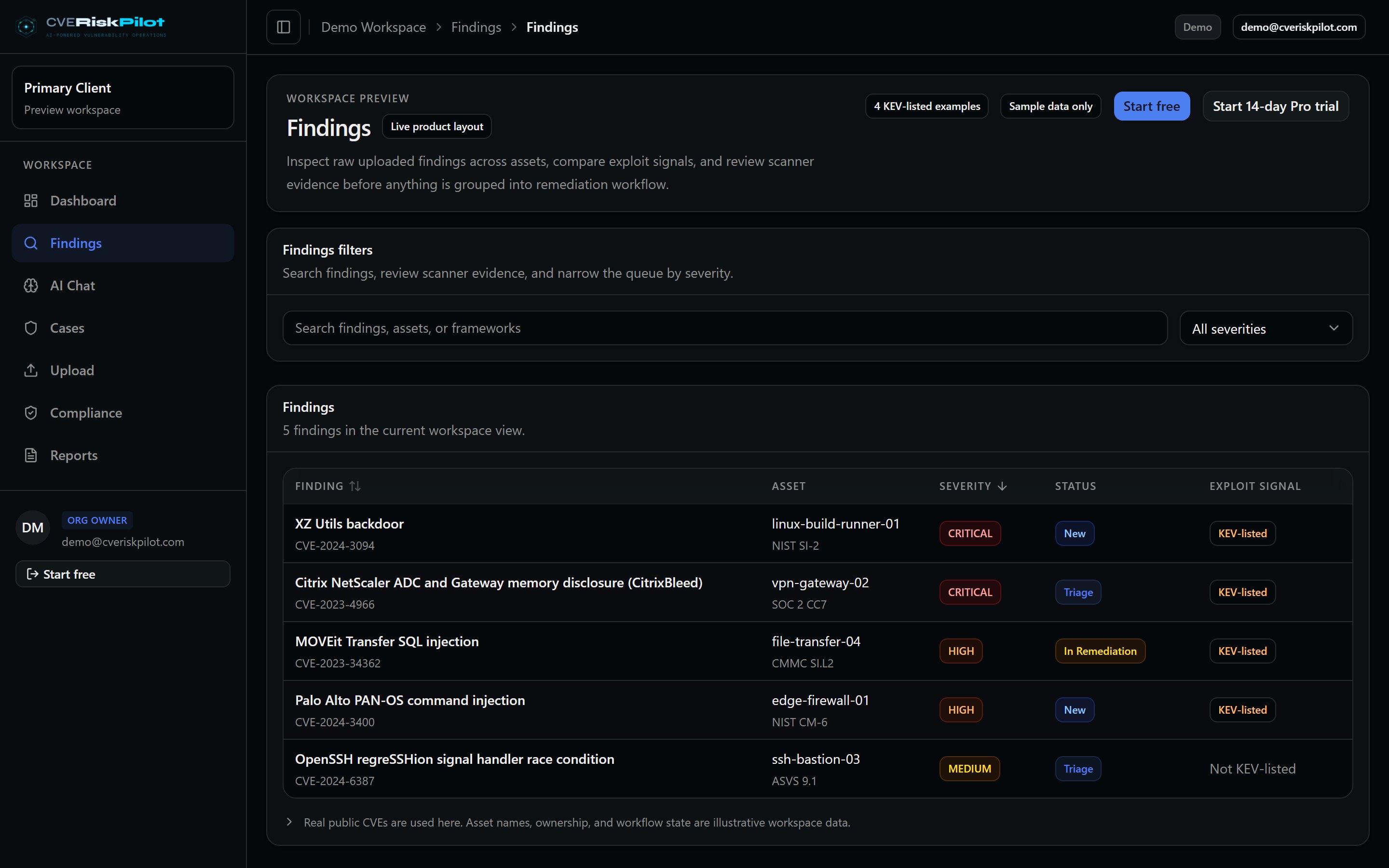
CVE triage queue
Each finding enriched with EPSS, CISA KEV, CWE, asset context, and compliance mapping.
Open live view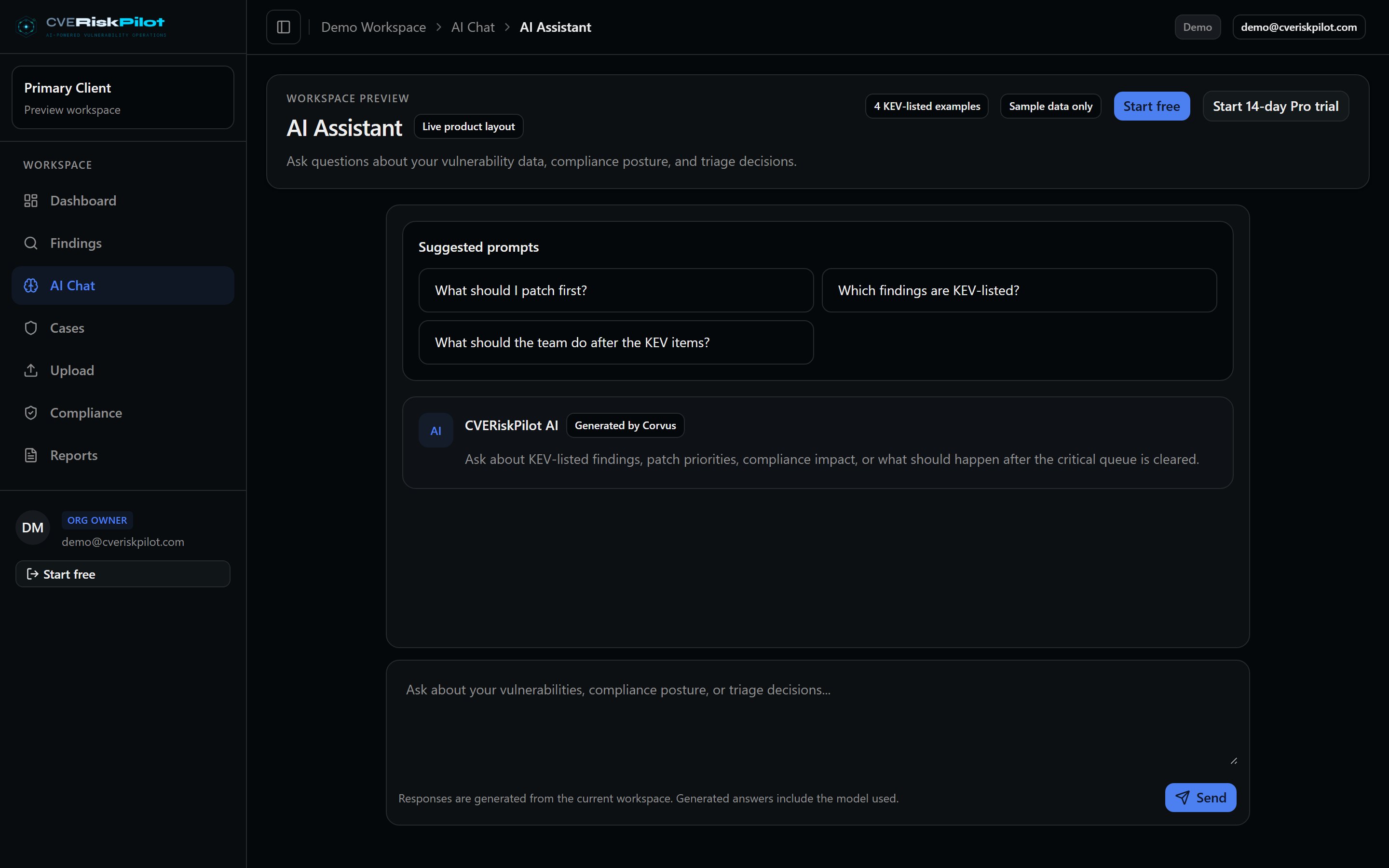
AI triage assistant
Corvus-backed triage with external AI fallback for complex cases. Ask questions in natural language.
Open live view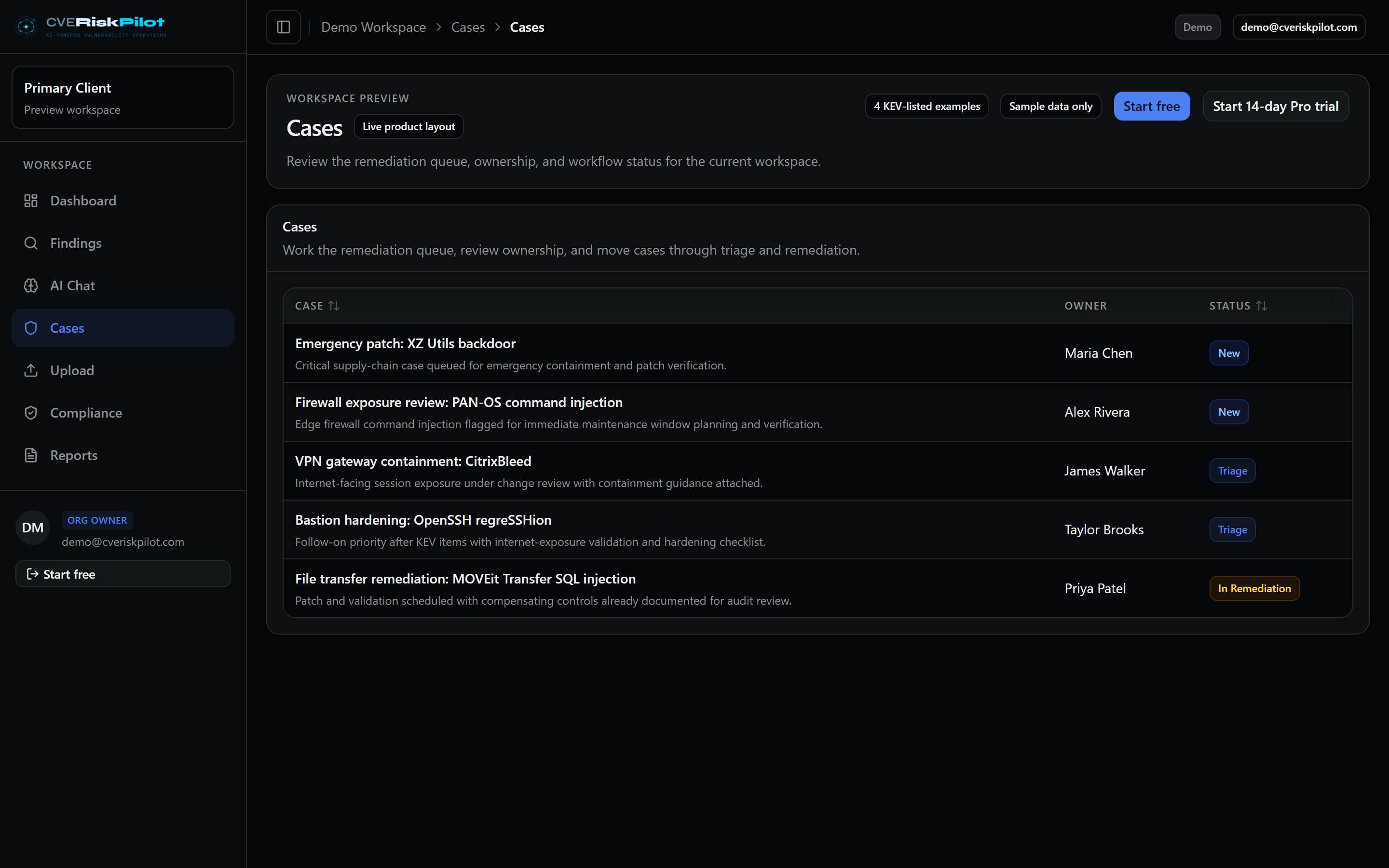
Case management
Risk acceptance, compensating controls, false-positive justification — audit-trailed.
Open live view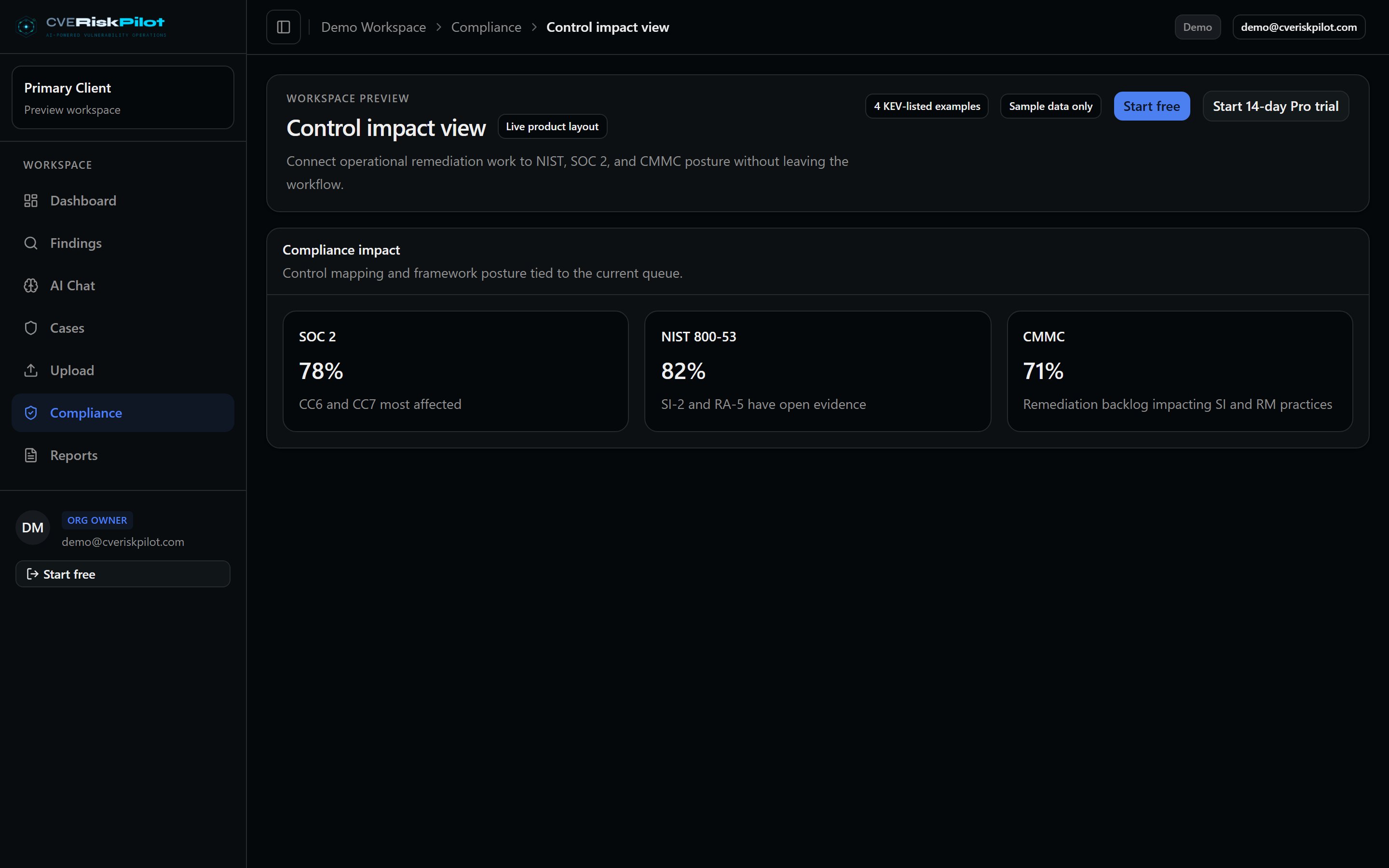
Compliance mapping
CWE-to-control bridge across 13 frameworks: NIST 800-53, SOC 2, CMMC, FedRAMP, HIPAA, PCI, ISO 27001 +.
Open live view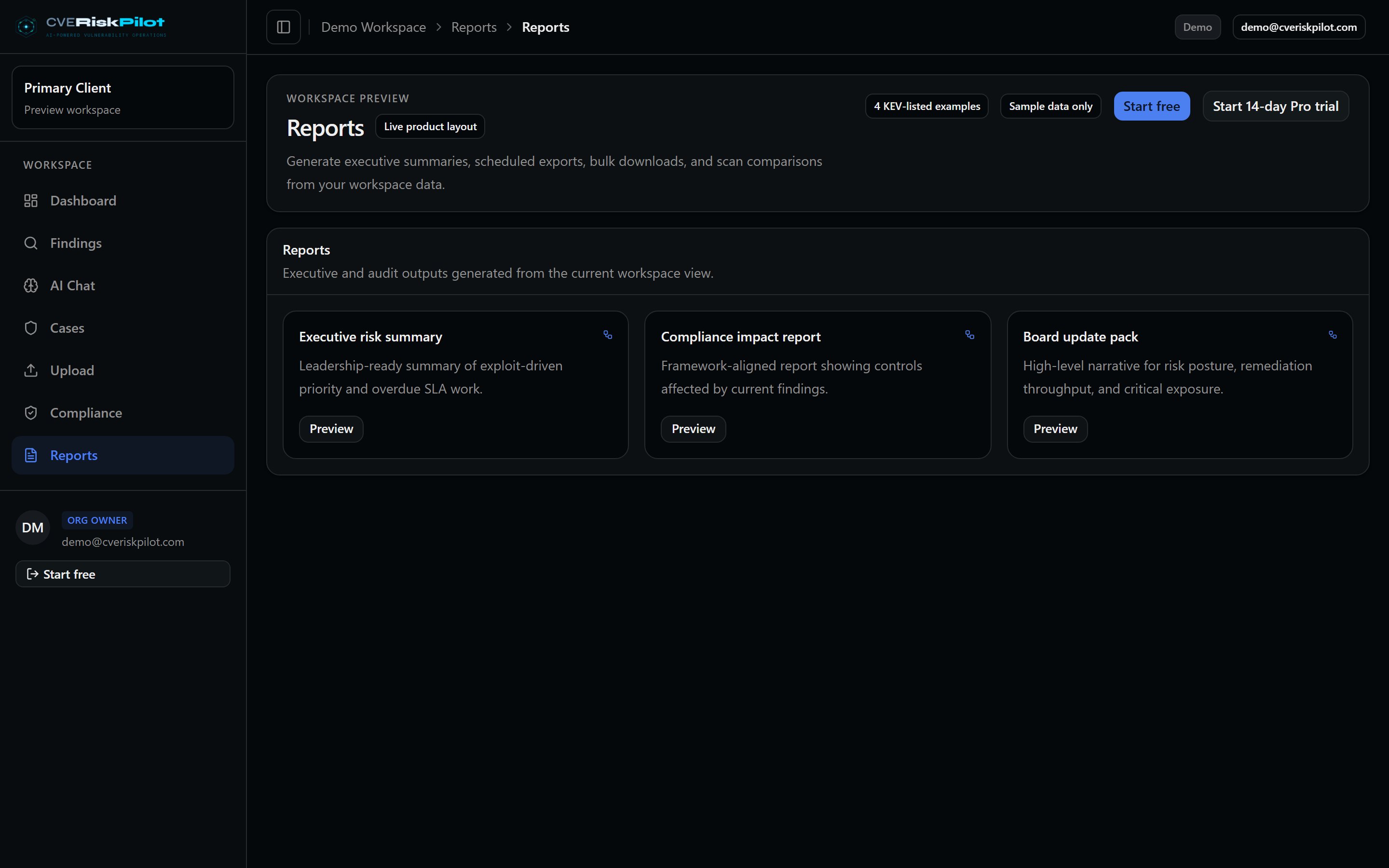
Audit-ready reports
POAM generation, evidence bundles, Vault Protocol cryptographic audit trail (Ed25519 + Merkle).
Open live viewImages are captured from the same code that ships to production — no mockups, no marketing stock.
Ingestion Layer
One platform. Every scanner you already use.
Don't replace your existing tools. CVERiskPilot sits on top of them, ingesting output from every major scanner in their native format and normalizing everything into one decision-ready model.
- 11 scanner format parsers (Nessus, SARIF, CycloneDX, Qualys, OpenVAS, SPDX, OSV, CSAF, CSV, JSON, XLSX)
- 5 scanner connectors (Tenable, Qualys, CrowdStrike, Rapid7, Snyk)
- CLI scanner with 13 package manager formats
- Signal Engine for real-time push ingestion via Pub/Sub
- SBOM import and correlation
Intelligence Layer
Stop treating every CVSS 9.8 the same.
Traditional tools dump a list sorted by CVSS. CVERiskPilot correlates each finding against exploit availability, CISA KEV status, EPSS probability, your asset criticality, and business context to produce a true risk score.
- NVD enrichment with CVSS vector parsing
- EPSS exploit probability scoring
- CISA KEV real-time correlation
- Asset criticality weighting
- AI-generated risk narratives and business impact statements
- Cortex Analytics for natural language compliance queries
AI Decision Layer
Guarded AI decisions, with a private-runtime path.
Production AI runs through explicit request paths with spend guards, redaction, and human review. Corvus is the private-runtime path for routine triage once serving and benchmark gates are healthy.
- Corvus private-runtime roadmap — buyer-facing claims gated by benchmark evidence
- Training data pipeline uses validated sources and reviewed human feedback exports
- Hybrid AI routing architecture — private fast path + guarded external escalation
- Human-in-the-loop feedback flywheel
- Risk acceptance workflows with approval gates
- POAM generation and PDF/CSV export
- "Not exploitable because..." risk statements
Compliance Mapping
Every finding mapped to 13 frameworks.
CVERiskPilot maps every vulnerability finding to the compliance controls it threatens. See your compliance posture score per framework and generate audit-ready evidence packages.
- NIST 800-53, CMMC, SOC 2, FedRAMP
- HIPAA, PCI DSS, ISO 27001, NIST CSF 2.0
- GDPR, ASVS, SSDF, EU CRA, NIS2
- CWE-to-control bridge for automated mapping
- Per-framework compliance posture scores
- Cross-framework impact analysis
Trust Layer
Cryptographic proof of every decision.
Vault Protocol provides Ed25519 digital signatures and Merkle tree integrity verification on every triage decision, approval, and audit event. Enterprise-grade evidence that withstands scrutiny.
- Ed25519 signing via hardware security module
- Merkle tree integrity verification
- Immutable audit trail with hash chaining
- Evidence collection for SOC 2 / CMMC / FedRAMP audits
- Tamper-evident compliance reporting
Action Layer
Push to the workflows your team already runs.
Move from triage to ticket without manual reformatting. Flux Pipelines let you build visual IF/THEN automation rules that route findings, assign ownership, and trigger notifications automatically.
- Jira and ServiceNow integration
- Visual automation rules engine (Flux Pipelines)
- Scheduled CVE intelligence digests
- Executive reports and evidence packages
- Webhook delivery with retry and tracking
- CSV and PDF export for all data
Compliance impact, per finding
Scanners tell you a CVE is critical. Compliance platforms tell you a framework is partially complete. CVERiskPilot connects the two: every finding shows which controls it threatens, and every remediation shows how posture improves.
- Scanners:
- “CVE-2024-1234, CVSS 9.8, in lodash.”
- GRC platforms:
- “SOC 2 — 78% complete.”
- CVERiskPilot:
- “This CVE affects 7 controls across 7 frameworks. Remediating moves SOC 2 from 78% to 82%.”
Finding detail
7 controls affectedPrototype Pollution in lodash
Remediation impact: SOC 2 score 78% → 82% across 7 controls in 7 frameworks.
See these features in action
Try the live demo with realistic data, or start free with your own scans. No credit card required.
